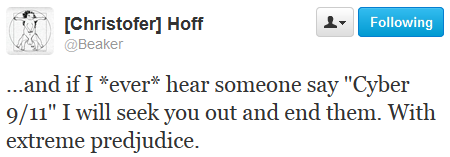

This is a rebuttal of sorts, to a tweet by @Beaker (10/18/2012) and a follow-up tweet by @Raistolo. This rebuttal basically wrote itself, as almost all of the data comes from the presentation "Cyberwar: Not what we were expecting" by @JoshCorman and myself.
While I am sure Beaker is not dropping his cloudy dealings to start a bedroom wall mural devoted to a psychotic plan to off government officials and pundits, his comment is eerily spot on. After his tweet, I replied saying he would be "very, very busy". Why is this spot on you ask? Glad I asked for you, since you are probably mildly curios if not completely apathetic.
 Many of us in the industry have been fighting the use of FUD-laced commentary,
disastrous buzz words, and fear-mongering flavor quotes. Invariably, they come from
politicians, money-seekers, charlatans, pundits, or morons that parrot the others. Dozens
of responsible and concerned InfoSec practitioners have tried to fight the
good fight, and lost. Decisively.
Many of us in the industry have been fighting the use of FUD-laced commentary,
disastrous buzz words, and fear-mongering flavor quotes. Invariably, they come from
politicians, money-seekers, charlatans, pundits, or morons that parrot the others. Dozens
of responsible and concerned InfoSec practitioners have tried to fight the
good fight, and lost. Decisively.
Beaker's comment struck a chord in me. We can't stop them from using these ridiculous terms; at least not all of them, often enough. The next best thing? End them. Of course, I am not going to take up arms to accomplish this, but I wouldn't lose any sleep over mentally deficient slime losing their careers, budgets, or anything else of value to them.
Sure, I don't have any real ideas on how to end their careers or budgets, but I firmly believe the community, if they honestly care about security, should seek a more rational voice that will shape the direction of security initiatives. Because it certainly isn't these Grade-A dipshits that will get billions of taxpayer dollars, only to offer up "joint initiatives" and "top-to-bottom reviews" that ultimately give us as much security as a padlock. Why am I over fighting them on these points? Because there is absolutely too much money to be made off the FUD.
If you have any doubt about the coming storm of cyber-spending, skim your headlines.
There you go! That is your encouragement to end them, give up on this shitty industry, or join them in making big bucks (and selling your soul). Now, for your gift; the start of your hit-list.
| Buzz Word | Source / Moron |
| Cyber 9/11 | "A cyber "September 11" has been predicted by Mike McConnell, a former director of the US National Security Agency." [source] |
| "Does a Cyber-9/11 Loom?" asks journalist Jason Bloomberg of CIO Magazine. [source] | |
| "[HP chief executive Meg] Whitman said that she believes a "cyber-attack of 9/11 scale" is likely to take place in the near future, while she was speaking at an HP customer event in London." [source] | |
| "We don't want a cyber 9/11," Senator Barbara Mikulski, D-Md., said, "right now, our adversaries are watching us." [source] | |
| Electronic Pearl Harbor | "CIA Director John Deutch warned yesterday that hackers could launch "electronic Pearl Harbor" cyber attacks on vital U.S. information systems." [source] |
| "Enter Jim Lewis, who directs the Technology and Public Policy Program at the Center for Strategic and International Studies, who says that the United States experienced its "electronic Pearl Harbor" in 2007." [source] | |
| "Richard Clarke, a senior counter-terrorism advisor under the Clinton and Bush Administrations, has written a book that warns that an .electronic Pearl Harbor. could bring the country to its knees in 15 minutes." [source] | |
| Electronic Hiroshima | "It is the US electronic Hiroshima in the Middle East. And it is the first time it is being done on such a large scale and so effectively." from a BBC archive [source] |
| "Jan 2011: Special Report: Stuxnet may be the Hiroshima of our time" writes David Gewirtz of ZDnet [source] | |
| "Stuxnet is the Hiroshima of cyber-war." writes Michael Joseph Gross of Vanity Fair [source] | |
| Cyber-apocolypse | "Both need to be addressed before Nimda and Slammer are followed by the third and fourth horsemen of our cyber apocalypse." writes BBC journalist Bill Thompson [source] |
| "Cyber-Apocalypse Now: Securing the Internet Against Cyberterrorism and Using Universal Jurisdiction as a Deterrent", a paper by Kelly A. Gable, Adjunct Professor of Public International Law, Drexel University Earle Mack School of Law. [source] | |
| Cyber-Hiroshima | "Stuxnet, the first military-grade cyberweapon known to the world, has been called a digital missile and a cyber-Hiroshima bomb." writes Mark Clayton of The Christian Science Monitor. [source] |
| "The only way to avoid a 'cybershima' scenario is to create an international agreement not to develop and not to share cyber-weapons." writes Dan Blum, Research VP at Gartner. [source] | |
| Cyber Atomic Bomb | "Toney Jennings, CEO of CoreTrace, adds that companies might have the equivalent of a 'cyber atomic bomb' in the server that .is not doing anything bad today." [source] |
| Cyber-Chernobyl | "Do we need a cyber-Chernobyl?" writes Lisa Myers of SCMagazine. [source] |
| Cyber Katrina | "U.S. Government to Put 'Cyber Katrina' to the Test" writes Paul F. Roberts of PC Magazine, a term representing "the digital equivalent of Hurricane Katrina". [source] |
| (bonus terminology clusterfuck) | "Cyber Tsunami 2.0: Digital Pearl Harbors, Cyber Riptides, & Swirling Cybersecurity Standards" by David Z. Bodenheimer of Crowell & Moring LLP. [source] |
As you can imagine, this is the tip of the iceberg.