
The International Information Systems Security Certification Consortium, Inc., (ISC)ý, bills themselves as "the global, not-for-profit leader in educating and certifying information security professionals throughout their careers." They are probably most well-known for their CISSPÛ - Certified Information Systems Security Professional. With 5 years of experience, practice in two of the ten domains they list and passing a 250 question multiple choice test, you can earn this certification.
The (ISC)ý Code of Ethics is founded on four canons to guide CISSP certification holders. I offer my own canons on the (ISC)ý Code of Ethics. These should be used to guide you in maintaining a better perspective on the absurdity that is (ISC)ý.
(ISC)ý bills the CISSP as a certification "for professionals who develop policies and procedures in information security." This wording makes it clear that managers and policy writers are the target demographic for the certification. For those in the trenches deploying firewalls, monitoring IDS, training users or performing security audits, this certification is not for you. Despite that, the industry as a whole has adopted this certification as some base-level for practitioners. This has led hundreds, if not thousands of professionals to obtain the certification as a method of getting a foot in the door or bypassing a company's initial HR screening. Further, many employers and customers will require the CISSP certification from employees and consultants, as if it represents some level of practical knowledge on a given domain.
For example, a penetration tester performs her craft based largely on personal experience. Most testers worth hiring are self-taught, using classes and books as a method to augment their knowledge rather than as a foundation for their skillset. A person may have a fifteen year career successfully performing penetration tests and security audits, without gaining any benefit from the CISSP (or any) certification. It certainly isn't required for that discipline, does not enhance their skillset and should not influence their ethics in performing services. So why would a company or customer want their auditor to have a certification that adds no value to the skillset of those that they employ?
One argument is to "weed out undesirables who have no knowledge of security". Perhaps a system administrator who wants to move into the realm of security does not have a good understanding of the depth and breadth of security disciplines. The CISSP certification would conceivably help ensure that individual has a base level of knowledge. In reality, it doesn't mean any such thing. With the number of CISSP bootcamps, books on passing the test and readily available practice questions, it doesn't even require a reasonable amount of intelligence to pass the exam.
Everyone who made it through high school has some level of expertise in handling such tests. In this case, the CISSP exam is 250 questions covering 10 domains of security. The test is administered in a 6 hour time-frame, and each question comes with multiple-choice answers. There are many well-documented disadvantages to multiple-choice tests. One of these reasons, "they are more affordable for testing a large number of students", may strike to the heart of the matter; while (ISC)ý is a not-for-profit organization, that does not negate the incredible income generated from their certification process.
Consider that the CISSP is one of nine certifications they offer. To take the CISSP certification exam, it costs up to US$599 and then US$85 each year for three years during the "certification cycle". That is US$854 for each person that obtains the CISSP. As of August, 2010, there were 69,489 CISSPs across the world according to (ISC)ý. That gives us a rough figure of over US$59 million dollars taken in for issuing the certification (Note: the price of exam can be reduced by early registration and the price for exam and renewal has changed over the years). Such a large figure paints a clear picture for a strong motive in establishing a certification and pushing for widespread adoption, even if it has little to no bearing on the services offered by security professionals.
The not-for-profit (ISC)ý took in US$9.827 million in 2010, and US$9.452 million in 2009. The total assets for the company were US$25.303 million in 2010, and US$24.056 million in 2009. Is there any question as to who is getting the most value out of this certification?

Along with the shiny certification, you must also agree to adhere to the (ISC)ý Code Of Ethics. Guided by four canons, the code is actually more detailed. This code of ethics also comes with a wide variety of disclaimers and contradictions that immediately call into question their purpose and conviction.
On one hand, the steps for becoming CISSP certified say it involves "Subscribing to the (ISC)ý Code of Ethics - committing to and abiding by principles and guidelines set forth by (ISC)ý". The code of ethics page says that "members are required to commit to fully support this Code of Ethics (the "Code")", but also says the Code is "advisory rather than mandatory." The Applicant Endorsement Form says the applicant must "confirm that [they] will comply with "it" in the future", yet does not make clear if they must comply with the 4 canons or the Code of Ethics as outlined in the other PDF file. To make the wording have even less teeth, the Code of Ethics PDF essentially removes all responsibility as pertains to following the Code:
These objectives are provided for information only; the professional is not required or expected to agree with them. In resolving the choices that confront him or her, the professional should keep in mind that the guidance is advisory only. Compliance with the guidance is neither necessary nor sufficient for ethical conduct.
Compliance with the preamble and canons is mandatory. Conflicts between the canons should be resolved in the order of the canons. The canons are not equal and conflicts between them are not intended to create ethical binds.
The CISSP is not required or expected to agree with [the Code], consider it "guidance" and should not find it "necessary nor sufficient for ethical conduct". With all of those caveats, one must question the purpose of such a Code of Ethics. Of course, this is if you haven't already questioned the purpose of any such code of ethics. If a professional in our industry needs a written guideline on behaving ethically, is that someone we want working in our field? (ISC)ý even goes so far to suggest the same thing, citing "There are only four mandatory canons in the Code. By necessity, such high-level guidance is not intended to be a substitute for the ethical judgment of the professional." "By necessity" it stipulates, confirming that all things considered, ethical judgement should be left to the individual, not the Code. That said, why make someone agree to the Code in the first place?
Looking past the four general canons, the code of ethics gives a more detailed description of the ethics a CISSP agrees to abide by. By definition, "ethics" is a system of moral principles at the most fundamental level. After that, definitions begin to vary to account for the varied use of the term. For example, "the ethics of a culture", "rules of conduct [..] of human actions or a particular group" and "of an individual" are some distinctions. This reminds us that we may have a personal set of ethics, a set of ethics we follow as a law-abiding member of society and a set of ethics we adhere to as part of a professional organization. While these ethics are largely complementary, there are times when they will conflict.
In the case of the (ISC)ý code, areas of conflict are all too common. As such, the code quickly becomes counterproductive to a security professional that seeks to protect himself or his clients. This begins to explain the many disclaimers that the code is a guideline, isn't expected to be followed or even agreed with. Considering one of the four canons of their code is "Advance and protect the profession", the confusion in their own code works against this canon. From the Code of Ethics:
Canon:
- Provide diligent and competent service to principals.
Guidelines:
- Render only those services for which you are fully competent and qualified.
- Take care to be truthful, objective, cautious, and within your competence.
There is a strong theme of competence in the code. Rather than dig up links to hundreds of e-mails and forum posts that demonstrate CISSPs asking ridiculously stupid questions, I offer a challenge and will relate a brief story.
The Challenge - Ask a colleague that does not hold any (ISC)ý certification, that has been in the industry for at least five years (the same time required to obtain a CISSP) the following question: Have you encountered a CISSP in a position that was perceived as one with expertise (e.g., a consultant), in which the CISSP lacked basic knowledge of a security discipline that was relevant to the work being performed? I would wager that you only need ask a couple colleagues before you start hearing amusing and horrifying stories.
A Brief Story - Back in 1997, my second year as a security professional, I worked with a person who was one of the first couple hundred CISSP holders. This person was also a PhD holder in Information Security. He was on a small team providing security auditing and penetration testing to a large bank. The client had a wide variety of machines covering every conceivable platform. One of the most dominant in their environment was IBM's AIX, a proprietary Unix operating system. This CISSP and project leader was listening to several of the testers talk about their work that day. When I talked about getting root on over 20 of their AIX servers with the old "froot" bug, the CISSP gave me a quizzical look and sincerely asked me, "What is root?"
This was probably the first incident that truly sapped my optimism with regards to the future of the security industry. This story became one in a long history of similar stories that demonstrated to me personally, that many CISSP holders were not competent to perform work on a project to which they were assigned.
If a conflict of interest arises between (ISC)ý and a CISSP, will the code be used as a guideline to resolve the conflict? Or will the code of ethics be casually swept aside by the organization that seeks to impose it on their customers? A recent case demonstrates this exact ethical dilemma, and it paints a gruesome picture of how (ISC)ý operates and the lengths they will go to in order to prevail. The code of ethics has three guidelines that apply to this type of situation:
- Treat all members fairly. In resolving conflicts, consider public safety and duties to principals, individuals, and the profession in that order.
- Avoid conflicts of interest or the appearance thereof.
- Take care not to injure the reputation of other professionals through malice or indifference.
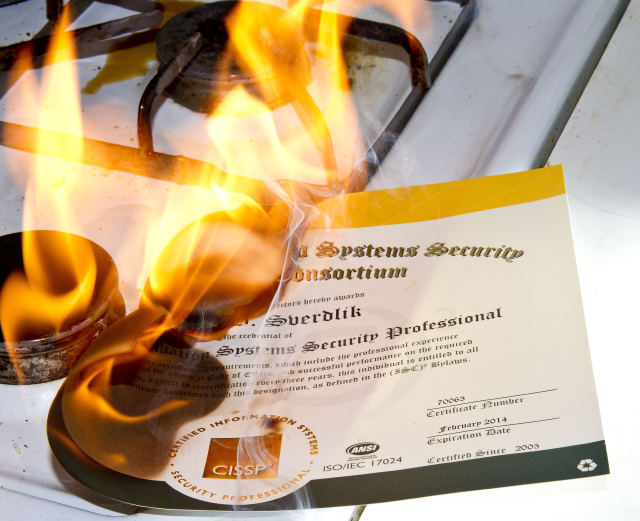
With these guidelines in mind, the case of (ISC)ý vs Boris Sverdlik becomes a poignant reminder of how (ISC)ý has failed to live up to their own mandated code of ethics. Sverdlik, more popularly known as "jadedsecurity" (@jadedsecurity on Twitter, jadedsecurity.net web site), gave a presentation at BSidesCT titled, and wrote part one & part two of a four part article titled "Hack the Interview". The methods described in this are not new in the context of interviews, regardless of industry. There are a wide variety of books on the topic, including one specifically tailored to programming interviews. Cold reading techniques have long been used by good and bad people. While it is associated more with so-called psychics and con men, it is equally used by law enforcement and profilers.
This presentation and article series set into motion a series of events that clearly shows that (ISC)ý, their general counsel and a former board member are vindictive and negligent.
On May 24, (ISC)ý general counsel Dorsey Morrow sent an e-mail complaint to Sverdlik saying that the Board of Directors received complaints about the article. Sverdlik immmediately challenged the position, citing examples of why such an article was perfectly acceptable. That same day, Morrow replied suggesting Sverdlik re-write the article in a different context. The next two mails in the sequence will be covered later in this article, as they breach another issue worth disclosing. Suffice it to say, Sverdlik did not re-write the article and held his ground. This frustrating dialogue with Morrow led Sverdlik to publish the emails and title the thread "Why I lost all respect for ISC2".
On June 30, after joking with his followers on Twitter, Sverdlik posted a parody image within the boundaries of U.S. Copyright fair use. Despite this, Morrow sent another complaint on July 1 saying that Sverdlik was "in breach of the Logo Usage Guidelines you agreed to". This prompted a quick reply in which Sverdlik once again held his ground and cited U.S. Copyright law to Morrow, the general counsel for (ISC)ý. The next reply from Morrow made a wild assumption that Sverdlik was located in Europe and cited EU registered trademark law. Morrow's final reply gives Sverdlik an ultimatum; remove the images or receive an ethics complaint and the possibility that (ISC)ý will pursue it further. Sverdlik replied, once again teaching the (ISC)ý general counsel about the difference between 'logo' and 'trademark' and U.S. copyright law, as Sverdlik is a U.S. citizen living in the continental United States.
At this point of the saga, things appear relatively simple. (ISC)ý feels that Sverdlik violated their trademark, also in violation of the agreed upon code of ethics. Sverdlik feels that the use of material is protected under copyright law. The next logical step for (ISC)ý, according to Morrow's last mail, would be to file an ethics complaint. The official complaint came on July 7, but the baffling thing is that it had nothing to do with the usage of trademark or logos. The complaint was filed by former (ISC)ý board member William H. Murray complaining about the "Hacking the Interview" article. Given that the last correspondence between Morrow and Sverdlik regarding the article was on May 24, an ethics complaint delivered July 7, six days after the trademark/logo dispute is suspicious. To several people, the timeline makes it clear that Morrow likely realized Sverdlik's stance on the trademark/logo were correct, and that (ISC)ý had no grounds to pursue him. Instead, (ISC)ý opted to go with an ethics complaint on the article 49 days after it was published (44 days after the last correspondence about it).
In the official complaint, it is important to note that Murray says "I have attached a writing of and by Boris Sverdlik, CISSP, writing under the pseudonym abhaxas, and published at [URL]" This accusation is curious as the URL Murray references makes no mention of "abhaxas". For those not familiar, abhaxas is the person who claimed credit for some of the PBS hacks. Given that Sverdlik blogged about it, it begins to explain how Murray may have associated the two names together, but Sverdlik has made it clear that they are different people. Regardless of what led to it, doing so is evidence of incompetence in the most basic of social forensics, and a libelous characterization. This action violates several canons and guidelines of the (ISC)ý code of ethics.
Another strong recurring theme in the ethics guidelines is that of associating with non-professionals, amateurs or criminals. For the sake of this article, I will lump all of those together in the category of "bad actors". From the guidelines:
- Avoid professional association with those whose practices or reputation might diminish the profession.
To discourage such behavior as:
- Professional association with non-professionals
- Professional recognition of or association with amateurs
- Associating or appearing to associate with criminals or criminal behavior
This part of the guidelines has long been a point of contention among many CISSP holders for obvious reasons. In the course of performing job duties, there are times when such guidelines are not only ridiculous, but counterproductive. Take for example anyone who works for or with law enforcement. There are plenty of cases where such association may be required as part of an investigation or undercover work. An instructor of a CISSP bootcamp must associate with the non-professionals s/he is teaching. If one wanted to be pedantic, the definition of criminal is "a person charged with and convicted of crime". Do you know anyone charged with speeding or running a stop sign, and pleading guilty? The definition of 'convicted' is "To find or prove (someone) guilty of an offense or crime, especially by the verdict of a court". Note the word "especially", meaning it does not have to come from a verdict of a court.
While one may be quick to dismiss these examples as rare cases or a technicality, they are just a few examples. If the primary argument against these examples is "a CISSP would know those are OK", then they don't need the guidelines to begin with. Instead of this convoluted and contradictory code of ethics, it could be replaced with "be ethical". Being around, associating with or even having a relationship with a bad actor does not automatically change who you are, or the ethics you hold. If a person's ethics are so easily swayed by a bad actor, then this guideline wouldn't have saved them. Despite all of this, (ISC)ý takes the absurdity one step further, into more libel.
In the previously mentioned email thread between (ISC)ý general counsel Dorsey Morrow and CISSP holder Boris Sverdlik, one of the replies from Morrow was unbelievable. Not only is the mail negligent and libelous, it demonstrates unprofessional behavior and a serious lack of knowledge about a landmark conference in the security industry. Underline added for emphasis:
From: Dorsey Morrow (domorrow@isc2.org) Date: Tue, May 24, 2011 at 11:26 AM Subject: RE: Inappropriate content To: Boris Sverdlik (bsverdlik[at]gmail.com) Boris, Indeed (ISC)ý does not condone or participate in Blackhat or Defcon. However, this does not logically conclude that this contributes to security failures such as Sony. To make such an argument means that we only find current and relevant infosec information at those venues, which is not true. While we do not condone or participate, neither do we prohibit members from attending if they believe it provides them an opportunity to learn, so long as they are not associating with or supporting criminal or unethical behavior typically associated with those venues. Nevertheless, that is not what is at issue. Of concern, is that the article is written as a "how to" for criminal behavior, not how to defend for professionals. I am not going to belabor the issue with you. I am simply going to suggest that you may be subject to a Code of Ethics complaint based on the content as presented in the article and would strongly urge that you rewrite to be more fitting for an infosec professional. Best regards, Dorsey Morrow, CISSPÛ-ISSMPÛ
The early days of Defcon certainly had its small share of questionable, unethical and illegal activity. This ranged from pranks (e.g., smoke bomb in the elevator) to late night hacking and phreaking (away from the convention though). When the Black Hat Briefings were created, founder Jeff Moss took several precautions to change the tone and purpose as compared to Defcon. The Briefings were held at a different hotel, had a significantly higher price tag, and catered to corporate, government and military attendees. The idea was to put a whole bunch of ethical people in the room with a so-called "black hat", so they could hear first hand how security was compromised, and learn how to protect against new and evolving threats. Since the first year of the Briefings, it has been a completely legitimate, mainstream corporate conference. Only in Morrow's fantasy world is criminal or unethical behavior associated with Black Hat Briefings.
This is backed by the fact CMP purchased Black Hat Inc. in 2005. Not included in the deal was the Defcon convention:
"DefCon is a separate company and a separate business. They [CMP] weren't interested in DefCon and I'd never sell it anyway. I don't think CMP wants to be in the underground hacker conference world," Moss said.
Labeling Black Hat in a way that claims it is associated with criminal or unethical behavior is libelous. Checking the 2011 Black Hat US speaker bios, we see that at least three CISSPs are presenting. Ironically, checking the Defcon 19 speaker page we find that eight CISSPs are presenting, and a ninth that is "working toward [the CISSP]". To add a dose of confusion to all of this, dozens of CISSP holders have submitted their attendance to Black Hat as Continuing Personal Education (CPE) credit, and had it approved by the (ISC)ý.
Morrow's libelous remarks toward CMP and the Black Hat Briefings are one case of unethical behavior more than I have ever seen at the conference, now going on 14 years and attended by more than 5,000 security professionals.

As a CISSP, you are bound to agree by the code of ethics. You are also bound to report actions or behavior that violates the code. To facilitate this, (ISC)ý has an Ethics Complaint Procedure that must be followed. Looking through the procedure and reading their caveats, it is clear that the burden is on the side of the accuser, like the U.S. justice system. However, there are several aspects that are an outright burden to the good guy (the person complaining) and add an extra layer of protection for the bad guy (the CISSP violating the code of ethics). A few items from the procedure (last item in bold as (ISC)ý does):
While disclosure of the identity of the complainant will be avoided where possible, upon filing a complaint, the complainant implies consent to disclose his identity to the respondent, where the board or its agents deem it necessary for due process.
In private email between Morrow and myself, he has indicated that a complaint does not guarantee that the complainant name will be given to the accused, but admits that it is a possibility if the board feels it necessary. This makes absolutely no sense. The evidence presented to the board about the unethical actions of a CISSP holder should stand on their own, and should have relevance to the individual complaining unless they have been directly hurt, and their evidence includes their name. (ISC)ý should offer the option to guarantee they will withhold the complainant name, so as to encourage people to report unethical behavior. Otherwise, professionals may avoid making a formal complaint to avoid the drama or potential backlash should the target of the complaint seek revenge in some fashion.
Standing of Complainant
Complaints will be accepted only from those who claim to be injured by the alleged behavior. While any member of the public may complain about a breach of Canons I or II, only principals (those with an employer/contractor relationship with the certificate holder) may complain about violations of Canons III, and only other professionals (those who are certified or licensed as a professional AND also subscribe to a code of ethics) may complain about violations of Canon IV.
As a reminder, the (ISC)ý Code of Ethics Canons:
* Protect society, the commonwealth, and the infrastructure.
* Act honorably, honestly, justly, responsibly, and legally.
* Provide diligent and competent service to principals.
* Advance and protect the profession.
Any member of the public, meaning someone who does not hold an (ISC)ý certification, can file a formal complaint about the breach of Canons I or II. Only principals, defined as "those with an employer/contractor relationship with the certificate holder", may file a formal complaint about the breach of Canon III. The most bizarre rule, only other "certified or licensed professionals that also subscribe to a code of ethics" may file a formal complaint about a breach of Canon IV.
Regarding Canon III, there are many times where an uncertified professional may be in a position to witness a breach of this canon. As a penetration tester, I was frequently contracted to do an independent test against systems that were just tested by another firm. This was done so the client had a gauge to determine how thorough the audit was, and to potentially uncover vulnerabilities that were not discovered. In such cases, I typically was provided access to the original report when writing my own, so that a comparison could be made and a list of missed findings presented. By the (ISC)ý rules, if I found a CISSP providing sub-par auditing, I could not file a complaint because I had no fiduciary relationship with the CISSP, only with the company that contracted them.
Regarding Canon IV, every human being subscribes to a code of ethics; their own. It may be more or less ethical than the convoluted ethics defined by (ISC)ý, but they do have their own ethical guideline. Ignoring that oddity, the requirement that a person be certified or licensed is ridiculous. After providing professional security services for 15 years (the first CISSP was issued 17 years ago), without a certification, I am somehow unqualified to determine when a person has breached this canon? The very nature of the Attrition Errata project, more specifically the Charlatans page, demonstrate the ability to document when a person is working in a manner that breaches Canon IV. Despite that, I am unable to file a formal complaint.
Got all that? In case the complaint guidelines are not clear, there is a handy complaint cheat sheet for professionals! Note: On March 28, 2006, in an email from Morrow to me, he said the following when I asked about "principal" as it was previously not defined in the code of ethics:
"Principal" is someone who has a fiduciary relationship with the CISSP (employer, contractor, or other agency relationship). I'm actually discussing modifying II with the Ethics Committee to include the general public. Seems the general public should be able to file a complaint under Canon II as well. But that is my interpretation.
The other noteworthy disclaimer provided by the board:
Neither the board nor its committee is an investigative body and neither has the authority to compel testimony. We can consider only evidence submitted to us voluntarily. There may be many cases where this evidence is not sufficient to support any action. We can proceed only where a prima facie case is made. Where no such case is made, the committee will close the complaint without prejudice to either party.
When submitting a notarized complaint (notary required, to ensure you "are serious" about the complaint), the argument must be made completely and fully. If the board decides that something is missing, unclear or debatable, they will not do any research on their own, may not send you additional questions and could very well close the complaint without further word. This could happen for a number of reasons; the board is too busy, seeks to protect revenue (CISSP renewal fees), personal bias or they just don't agree with the thoroughness of your complaint. Should your complaint be complete and accepted, the punishment levied on the offender is at the sole discretion of the board. This is curious because Morrow has told me that (ISC)ý cannot deviate from the published guidelines, as "the whole process is subject to attack, including every decision made as a result of that process", yet the process for discipline is NOT defined, completely subjective and closed to debate or question. No matter how legitimate the complaint is, the policy does not require the board to revoke the certification. Morrow has said there are "... a wide-range of sentences, from probation to the maximum sentence." The maximum sentence being, certification revocation.
As a practical example of the convoluted nature of the complaint procedure, take the case of Bill Hancock. Numerous complaints were made to (ISC)ý about Hancock, but none of them were formal notarized complaints. Despite that, (ISC)ý was asked to act on it given the overwhelming evidence and numerous people bringing him to their attention. They declined. Instead, they continued to associate with him, via his CISSP certification, despite that breaching the code of ethics.
Sponsor for professional advancement those best qualified. All other things equal, prefer those who are certified and who adhere to these canons. Avoid professional association with those whose practices or reputation might diminish the profession.
As an additional layer of protection against their own code, (ISC)ý board members and their general counsel can conveniently turn a blind eye to cases like Hancock. The code of ethics says "(ISC)ý members are obligated to follow the ethics complaint procedure upon observing any action by an (ISC)ý member that breach the Code." The key word here is observe. Even if the board has knowledge of unethical behavior, because they did not observe it first hand, they are not required to act on it. This is a technicality, but purposefully undermines the spirit of the code of ethics. Even the act of multiple people complaining about an individual, demonstrating that the person is hurting the CISSP brand and reputation, is not enough to warrant the board to act on it.
I don't imagine many CISSP holders made it to this part of the article. Based on personal experience with many (ISC)ý certified individuals, I firmly believe that the Dunning-Kruger effect will prevent them from considering the arguments outlined in this article. Previous criticism of the CISSP have covered the value and thoroughness of the test. A more recent op-ed succinctly summarizes the attitude and elitism that seems to surround the CISSP and security certification in general.
Moving forward, I encourage every security practitioner to be aware of their (ISC)ý certified peers' actions. Should one of them step out of line and break the code of ethics they agreed to, take the time to file a formal complaint and see if (ISC)ý handles it in a professional and ethical manner. In the course of research for this article, I have four clear cases of a CISSP violating the code of ethics and will be lodging formal complaints.
The high road of ethics that (ISC)ý flaunts is just as muddy as the trenches filled with the uncertified masses striving to do good.
He that would govern others, first should be Master of himself. - The Bondman, act I, sc. iii
Copyright 2011 by Brian Martin. Permission is granted to quote, reprint or redistribute provided the text is not altered, appropriate credit is given and a link to the original copy is included.
Should you appreciate the article and feel generous, please donate a couple of bucks to any 501(c)(3) non-profit that benefits animals or computer security on our behalf.